انجمن مدیران و راهبران شبکه
Network Managers and Administratorsانجمن مدیران و راهبران شبکه
Network Managers and Administrators9 Immutable Laws of Network Design
9 Immutable Laws of Network Design
Follow these simple rules to ensure your network is stable, secure and built to last as you overlay new services and applications.
Each year, my company has the opportunity to work with many clients on their network architectures, designs and configurations. We also work with clients when they have network issues and need troubleshooting assistance. Based on those many years of experience with a variety of environments and customers, I've developed this list of nine immutable laws of network design.
Following these simple rules helps you create and maintain a stable, long-lasting network infrastructure that will be invaluable as your organization begins to overlay additional services or applications. Whether you’re redesigning for wireless, preparing for software-defined networking (SDN) or simply expanding your virtualized environments, designing by these rules will increase the stability, manageability and security of your network.
1. Know, Don’t Guess
Two phrases uttered frequently during network design are “I’m pretty sure” and “I think.” As a professional tasked with discovering, researching and documenting client networks, I can tell you those phrases don’t cut it in our organization, and they shouldn’t be accepted in yours. There’s more than a 50% chance what you think you know is wrong. Networks are inherited, many admins may touch them, and they’re frequently changed in a fit of fury, troubleshooting or testing. When documenting a network or committing even a minor change, you should always look, verify and know--never guess. The mantra in our office is, “No information is better than wrong information.”
2. Avoid Dangling Networks
As SDN, virtualization and application-based technologies creep into our networks, we need to take a hard look at configuration sprawl and prepare for a massive cleanup. Avoid dangling and mismatched networks and VLANs throughout the infrastructure. It’s not unusual to see VLANs tagged where they should be untagged, or a VLAN dead end into an untagged VLAN. There are some instances of think-outside-the-box moments where a configuration like this is needed, either for a transition period or to work around a specific situation, but the practice should be the exception, not the rule.
3. Route Where Needed, Not Where Possible
Routing at the edge sounds like an advanced approach to network architecture, but it can cause more problems than it solves. Sure, you may get some additional speed, but in most networks, that speed will never be measurable, and the complexities of overly distributed routing lead to management and security headaches.
4. See All, Manage All
You certainly can’t manage what you can’t see. Visibility into the network has always been important, and it’s going to be even more essential as networks evolve to solve the demands of virtualization and applications. Know what you have, where it is, and monitor it constantly.
5. Know When To Standardize
There are times when standardizing offers great advantages, and other times when it will be working at cross-purposes to your objectives. This might mean standardizing on a single vendor for interoperability, or it may mean standardizing on configurations, security settings and management. Either way, make sure your choice is serving a purpose and providing flexibility as your network grows in the future. Don’t get pigeonholed in to a single-vendor solution when the costs outweigh the benefits, and don’t miss opportunities to standardize on platforms that can increase effectiveness of management and security.
[ Common errors like mismatched masks and duplicate IPs can spell disaster on a network. Find out the top mistakes to avoid in "The 10 Deadliest Networking Mistakes."]
6. Layer 1 Is King
Your sleek new infrastructure of VLANs and virtual devices is complete trash if the foundation of your network is faulty. Layer 1 is king, and disruptions in Layer 1 still contribute to a huge volume of detrimental network outages. As network capabilities develop and grow, Layer 1 requirements will evolve and remain the most critical consideration.
7. Simple Always Wins
Just because you can do it doesn’t mean you should. Labs and test environments are the place to play and think outside the box with your configurations. In an enterprise production environment, you’re best served following the K.I.S.S. model, and keeping your network as simple as it can be while maintaining the required connectivity and security.
8. Power Is Important
To say we’ve been spoiled in recent decades with our power sources seems strange, but it’s true. As power demands increase with newer technology, availability and consistency of power is more critical than ever. The addition of virtualized machines and software-based appliances that are more sensitive to power issues compounds the problem. Oftentimes, power issues can cause widespread network disruptions without ever triggering an alert. Clean, conditioned, consistent power used to be a luxury, but is now a necessity in the network.
9. Embrace Documentation
You may have flashbacks of writing book reports in high school, but maintaining documentation on your network is the easiest way to ensure you’re following best practices, tracking changes and creating the means to troubleshoot effectively. As we layer on more technology and applications, documentation will increase in significance. Embrace it, live it, love it, do it. Twenty minutes of documentation now, even if you feel you don’t have 20 minutes to spare, may save you 20 hours down the road.

پیکربندی تانل IP-SEC بصورت Site-To-Site VPN بر روی لینک Point To Point بین دو روتر سیسکو
پیکربندی تانل IP-SEC بصورت Site-To-Site VPN بر روی لینک Point To Point بین دو روتر سیسکو
سلام 
مطلبی که امروز تو این پست خدمتتون ارائه می کنم در حقیقت بازخوانی روایتیست از ویدئوی آموزشی جناب آقای Eric Spengler که در آرشیو YouTube به آدرس https://www.youtube.com/watch?v=aJB0E3_C4dQ و به شیوه بسیار شیوا و روان و البته فقط در حد اطلاعات لازم و کافی ارائه شده است.
لذا در این قسمت ضمن بازخوانی مجدد مطالب این فیلم آموزشی، قصد دارم با تجزیه و تحلیل زوایای فنی دستورات بکار رفته در پیکربندی IP-SEC ، با دقت و تمرکز بیشتری بصورت گام به گام در صدد درک بهتر نحوه پیکربندی این مکانیزم امنیتی برآییم.
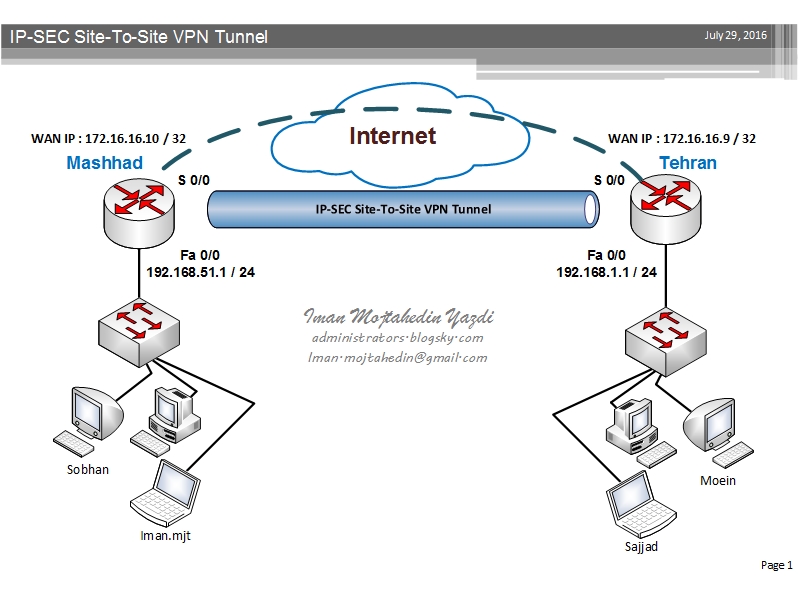
طبق اطلاعات عنوان شده در این ویدئو، پیکربندی تانل IP-SEC بصورت Site-To-Site VPN شامل 5 مرحله به شرح موارد زیر میباشد:
- مرحله اول: پیکربندی ISAKMP Policy که طی آن پارامتر های مختص به فاز اول ایجاد تانل IP-SEC یعنی مرحله برقراری Trust relation sheep بصورت تنظیم Pre-Shared key یا Certificate مشخص و در هر دوطرف تنظیم می گردد.
- مرحله دوم: پیکربندی Transform set که در جریان آن پارامتر های مربوط به فاز دوم تانل IP-SEC و متد Encryption ، سایز کلید و الگوریتم Hashing مورد استفاده در جهت رمزنگاری داده های عبوری از داخل تانل مشخص می شوند.
- مرحله سوم: مشخص نمودن ترافیک عبوری از داخل تانل از طریق تعریف Access-List می باشد.
- مرحله چهارم: تعریف Crypto MAP جمع بندی و تعریف روابط بین پارامتر های تعریف شده در مراحل قبل خواهد بود.
- مرحله پنجم: و آخرین قدم در بهره برداری از تانل امن IP-SEC شامل مشخص نمودن اینترفیس فیزیکی یا GRE Tunnel ی خواهد بود که قرار است ترافیک تانل IP-SEC از طریق آن به سمت روتر طرف مقابل هدایت شود.
Step By Step configuration of site-to-site IP-SEC VPN tunnel:
!========== phase 1 ================================
crypto isakmp policy 10
encr aes 256
authentication pre-share
group 5
lifetime 3600
crypto isakmp key imanP@SS address 172.16.16.10
!
crypto ipsec security-association lifetime seconds 1800
!
!========== phase 2 ================================
crypto ipsec transform-set TRNFSiman esp-aes 256 esp-sha-hmac
!========== phase 3 ================================
crypto map CMAP 10 ipsec-isakmp
set peer 172.16.16.10
set security-association lifetime seconds 900
set transform-set TRNFSiman
match address 123
!========== phase 4 ================================
access-list 123 permit ip 192.168.1.0 0.0.0.255 192.168.51.0 0.0.0.255
!========== phase 5 ================================
ip route 192.168.51.0 255.255.255.0 FastEthernet0/0
!========== Last step ==============================
TEHRAN(config)#interface fastEthernet 0/1
TEHRAN(config-if)#crypto map CMAP
جهت ارزیابی و پایش وضعیت تانل و بررسی ترافیک انتقال داده شده از روی آن می توانید از دستورات زیر استفاده کنید:
همایش شبکه و امنیت در محیط سازمانی با مدیریت اداره کل ارتباطات وفناوری اطلاعات استان بوشهر
 |
همایش شبکه و امنیت در محیط سازمانی با مدیریت اداره کل ارتباطات وفناوری اطلاعات استان بوشهر وهمکاری دانشگاه فردوسی مشهد در استان بوشهر برگزار گردید.
به گزارش روابط عمومی اداره کل ارتباطات وفناوری اطلاعات استان بوشهر،این اداره کل در راستای نهادینه کردن امنیت در فناوری اطلاعات با همکاری سازمان فناوری اطلاعات و مرکز آپای دانشگاه فردوسی مشهد این کارگاه آموزشی را در حوزه امنیت برگزارنمود.
قابل ذکر است همزمان با برگزاری کارگاه امنیت، مرکز آپای دانشگاهی نیز افتتاح یافت که بدین منظور جناب آقای مهندس سجادی معاون محترم امنیت سازمان فناوری اطلاعات ایران نیز ضمن حضور در دانشگاه خلیج فارس بوشهر، در کارگاه امنیت حضور یافتند و نکاتی را در خصوص الزامات امنیتی در سازمانها و وظایف مراکز آپا بیان فرمودند.


:::::::::::: لینک مستقیم خبر در وب سایت وزارت ارتباطات و فنآوری اطلاعات ............
دانلود IOS های جدید سوئیچ های سری Cisco catalyst 2960 و Cisco catalyst 3750e
سلام صبح بخیر 
بنا بر درخواست بسیاری از دوستان و همکاران، آخرین نسخه IOS مربوط به دو سوئیچ متداول Cisco catalyst 2960 و Cisco catalyst 3750e رو برای استفاده شما دوستان از وب سایت شرکت Cisco دانلود کردم که می تونید از این قسمت دانلود نمایید.

| Description: | LAN BASE |
| Release: | 15.2.2E5 |
| Release Date: | 07/Jun/2016 |
| File Name: | c2960-lanbasek9-mz.152-2.E5.bin |
| Min Memory: | DRAM 128 MB Flash 64 MB |
| Size: | 13.96 MB (14635349 bytes) |
| MD5 Checksum: | 4ab00188887e9844bd8d1db83adbbf20 |
| Description: | IP BASE |
| Release: | 15.0.2-SE10 |
| Release Date: | 21/Jul/2016 |
| File Name: | c3750e-ipbasek9-mz.150-2.SE10.bin |
| Min Memory: | DRAM 256 MB Flash 64 MB |
| Size: | 19.49 MB (20432128 bytes) |
| MD5 Checksum: | 9146e34146a53662a42af28d272789fb |
دوره آموزشی شبکه و امنیت اطلاعات در سازمانها در استان خراسان شمالی
دوره آموزشی شبکه و امنیت اطلاعات در سازمان ها،
اداره کل ارتباطات و فنآوری اطلاعات استان خراسان شمالی.
..::: لینک مستقیم خبر در وب سایت وزارت ارتباطات و فنآوری اطلاعات :::..
به همت اداره کل ارتباطات و فناوری اطلاعات استان خراسان شمالی ؛ با همکاری سازمان فناوری اطلاعات ایران و سازمان مدیریت و برنامه ریزی استان ؛ دوره آموزشی شبکه و امنیت اطلاعات در سازمانها با اعطای گواهینامه ویژه مدیران وکارشناسان فناوری دستگاه ها و سازمان های استان در محل دانشگاه بجنورد برگزار شد.

پایان گزارش :::..